Mobile applications increasingly operate in adversarial environments. Banking apps are reverse-engineered to extract API keys, gaming platforms are manipulated to bypass in-app purchase gates, and security-sensitive enterprise tools face runtime tampering via instrumentation frameworks. Root and emulator detection has evolved from a niche hardening technique into a fundamental pillar of mobile application defense — but it carries a complicated set of trade-offs that engineers and product teams routinely underestimate.
Root detection refers to the practice of identifying whether the device running your application has had its operating system's trust boundary compromised — either through Android rooting or iOS jailbreaking. Emulator detection, while technically distinct, shares the same threat model: both scenarios remove the hardware attestation that guarantees that app sandboxing is built upon. An attacker with root access or an emulated environment can inspect memory, patch binaries at runtime, intercept network calls at the system level, and automate behavior that would otherwise require physical hardware at scale.
This article is not a case for or against implementing these detections wholesale. The engineering reality is that root and emulator detection is a spectrum — from lightweight checks used for telemetry to aggressive blocking logic that becomes a battlefield between your app and the security research community. Understanding what each detection strategy buys you, at what cost, and in what context it is appropriate, is the entire point.
Foundational Concepts
To reason precisely about detection, you need to understand what you are actually detecting. A rooted Android device is one where the user or an attacker has obtained superuser (UID 0) access to the underlying Linux kernel, typically by flashing a custom recovery image, exploiting a kernel vulnerability, or unlocking the bootloader and installing a root management tool such as Magisk. This breaks Android's application sandbox: processes that would normally be isolated can now read each other's memory, write to protected directories, and hook into system calls via kernel modules.
iOS jailbreaking follows a similar threat model but operates differently at the platform layer. Apple's Secure Enclave and code-signing requirements mean that jailbreaks typically exploit kernel vulnerabilities or userland exploits to gain unsandboxed code execution and bypass code integrity enforcement. The result is equivalent: an app can no longer assume that its sandbox boundaries are intact, that its binary has not been patched in memory, or that system APIs return honest values.
Emulator detection, by contrast, targets a different attack surface. Android emulators — particularly those running on x86 architectures with hardware acceleration — are heavily used by mobile automation frameworks, fraud rings running click farms, account farming operations, and reverse engineers who want a more controllable environment than a physical device. The detection goal is to identify device fingerprints, hardware characteristics, and runtime behaviors that are specific to emulated environments and absent from real consumer hardware.
A critical nuance is that these detection categories overlap in threat profile but diverge sharply in false positive risk and bypass difficulty. Rooted devices are actively carried by security researchers, penetration testers, power users, and developers. Emulators are routinely used by your own QA engineers and CI/CD pipelines. Any enforcement logic that acts on these detections must account for the population of legitimate users it will affect.
- Root grants UID 0 access, breaking Android's process sandbox
- Jailbreaking bypasses iOS code-signing and Secure Enclave guarantees
- Emulators expose automation attack surfaces including account farming and click fraud
- Detection accuracy and false positive risk vary significantly across device populations
- Enforcement decisions must be decoupled from detection logic to allow policy flexibility
Why It Matters in Modern Mobile Development
The threat landscape for mobile applications has matured considerably. Early mobile security thinking was largely about network transport — TLS certificate pinning, encrypted payloads, token expiry. These remain important, but a rooted device or an instrumentation framework like Frida completely undermines network-layer protections: if an attacker can hook the SSL_read function at the system level, certificate pinning is irrelevant. Root and emulator detection is specifically valuable because it raises the cost of attacks that target the client runtime rather than the network.
For financial applications, the stakes are concrete. Mobile banking fraud increasingly relies on overlay attacks, accessibility service abuse, and runtime hooking to steal credentials or authorize fraudulent transactions without the user's knowledge. Most of these attack vectors require either root access or a controlled emulated environment to operate at scale. Detection does not prevent a determined attacker with unlimited time and resources, but it substantially increases the cost of mass exploitation — which is the relevant threat model for fraud operations.
For enterprise mobility management (EMM) use cases, root detection intersects with compliance requirements. Regulated industries often require that devices accessing corporate data be in a known-good state. Google's Android SafetyNet / Play Integrity API provides hardware-backed attestation that goes beyond what in-app detection can achieve, making it the preferred mechanism for scenarios requiring auditability.
In gaming and competitive applications, emulator detection is often about enforcement fairness rather than security in the strict sense. Bots operating via emulated environments can farm resources, manipulate leaderboards, and degrade the experience for legitimate players. Detection here feeds into anti-cheat infrastructure rather than security policy.
- Root/jailbreak bypasses network-level protections entirely when hooking at the system call layer
- Financial fraud increasingly targets client runtimes rather than network channels
- Hardware-backed attestation (Play Integrity, DeviceCheck) is stronger than in-app heuristics alone
- Gaming and competitive apps use emulator detection primarily for fairness enforcement
- Enterprise compliance requirements often mandate device integrity checks as a policy prerequisite
Architecture & System Design Breakdown
A production-grade detection system is not a single function call. It is a layered architecture that collects signals, aggregates them into a confidence score, and feeds that score into a policy engine that determines how the application responds. The key architectural principle is separation of detection from enforcement. Collapsing these two concerns into a single function — 'if rooted, crash' — is both fragile and operationally dangerous. A layered approach allows you to adjust enforcement thresholds, add new signals, and respond to bypass techniques without redeploying your binary.
The signal collection layer sits closest to the OS and hardware. It gathers indicators across several dimensions: filesystem artifacts left by root management tools, process listings that include known hooking frameworks, build property anomalies, hardware characteristics that differ from real devices, and behavioral signals gathered over time. These signals have varying reliability — some are deterministic (a specific file either exists or it does not), others are probabilistic (a combination of hardware properties that is statistically implausible for a real device).
The aggregation layer normalizes these signals into a risk score. A single file-system artifact indicating root may be a false positive from a legitimate root management tool used by a developer; five corroborating signals across different dimensions make a much stronger case. This is where machine learning approaches can outperform static rule sets, particularly for emulator detection where the landscape of virtualization platforms evolves continuously.
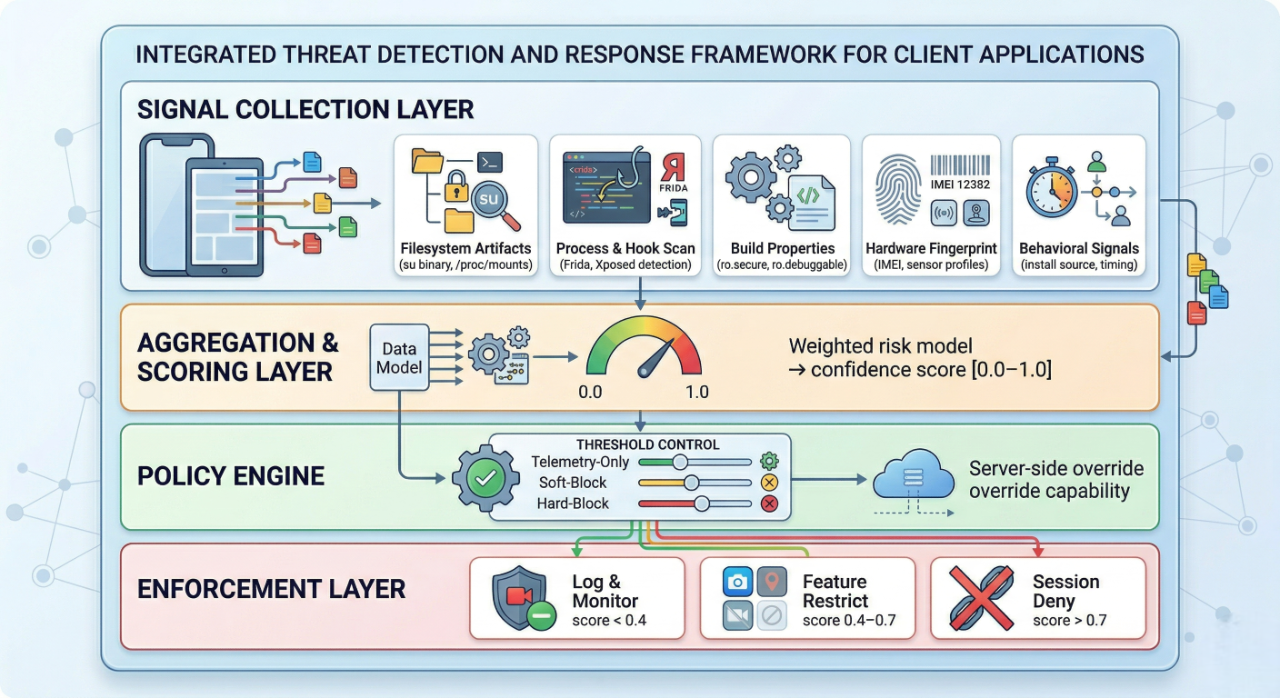
The policy engine is intentionally server-side in mature implementations. Hardcoded thresholds in your binary can be discovered and patched by a motivated attacker; server-side policy allows you to respond to a bypass technique in hours rather than weeks. At a minimum, the threshold that controls enforcement behavior should be configurable via a backend flag, separate from your standard feature flag system, with appropriate access controls.
Implementation Deep Dive
Implementing root and emulator detection at a production level involves combining multiple independent signals. No single check is sufficient — each can be bypassed in isolation. The defensive value comes from depth: the cost of bypassing 12 independent signals simultaneously is substantially higher than bypassing any one of them. The following workflow reflects how a well-structured implementation is typically assembled.
- Define your threat model explicitly. Identify what attack classes you are defending against — runtime instrumentation, automated fraud, reverse engineering — and derive the signal set from that model rather than copying an open-source checklist without understanding it.
- Implement static artifact checks. On Android, check for the presence of su binaries across multiple paths (/system/bin/su, /system/xbin/su, /sbin/su, /data/local/xbin/su), Magisk-related directories and mount points, and the Busybox binary. These checks are cheap and catch unsophisticated environments.
- Check build and system properties. Values like ro.secure=0, ro.debuggable=1, and ro.build.tags containing 'test-keys' indicate development or modified builds. Read these via Android's SystemProperties class rather than running shell commands, which is slower and more detectable.
- Scan for known instrumentation frameworks. Check the loaded libraries list in /proc/self/maps for Frida gadget strings, and check for Xposed-related classes in the ClassLoader. These checks will evolve as frameworks update their evasion techniques — treat them as a versioned component that requires regular maintenance.
- Aggregate signals into a risk score and transmit to your backend. Avoid making enforcement decisions purely client-side. The scored payload should be signed with a client secret (obfuscated) to prevent trivial replay attacks.
- Implement policy-driven enforcement server-side. The server decides whether the session proceeds, is restricted, or is terminated — and can update those thresholds without a binary deployment.
// Android: quick ro.secure property read
val isSecureBuild = try {
val cls = Class.forName("android.os.SystemProperties")
val get = cls.getMethod("get", String::class.java, String::class.java)
get.invoke(null, "ro.secure", "1") as String == "1"
} catch (e: Exception) { true }
// iOS: check for cydia:// scheme (jailbreak indicator)
let isCydiaPresent = UIApplication.shared.canOpenURL(
URL(string: "cydia://package/com.example")!)
On iOS, detection signals differ because the platform architecture is fundamentally different. Common checks include testing whether the Cydia app scheme is openable (cydia://), attempting to write outside the app sandbox to paths like /private/jailbreak_test.txt, checking for the existence of known jailbreak-related files (/Applications/Cydia.app, /usr/bin/ssh, /etc/apt), and verifying that fork() fails as expected in a sandboxed process. Apple's own DeviceCheck and App Attest frameworks provide hardware-rooted attestation that is significantly harder to bypass than in-app heuristics.
Apple's App Attest framework documentation provides a comprehensive reference for implementing hardware-backed device attestation, which should be the baseline for high-security iOS applications.
Advanced Patterns & Optimization
Sophisticated adversaries do not attempt to disable detection outright — they attempt to appear legitimate. Magisk's MagiskHide (and its successors like Zygisk deny lists) specifically hides root artifacts from targeted application processes. Frida's --runtime=v8 mode patches its gadget strings to evade naive string scanning. This means your detection logic must evolve continuously and should employ techniques that are harder to target for selective evasion.
One of the most effective advanced patterns is behavioral anomaly detection. Rather than checking for specific artifacts — which can be hidden — you measure properties of the runtime that are difficult to forge: the timing characteristics of cryptographic operations (which differ in virtualized environments), the consistency of hardware sensor data over time, the statistical distribution of inter-process communication latency, and the presence of timing artifacts introduced by dynamic binary instrumentation. These behavioral signals are much harder to suppress than static file paths.
Code integrity verification adds another dimension. On Android, you can verify the APK signature against a known-good value at runtime, detect if your own DEX bytecode has been modified, and check whether the ClassLoader chain has been tampered with. On iOS, App Attest's cryptographic key attestation provides a hardware-rooted guarantee that goes beyond anything achievable in user space. The key architectural insight is that your most sensitive operations — key derivation, payment authorization, biometric verification flows — should require a fresh attestation token, not a session-level flag.
- Use behavioral timing analysis to detect instrumentation without relying on scannable string artifacts
- Implement code integrity verification as a periodic in-session check, not just at launch
- Require fresh attestation tokens for high-value operations rather than relying on session-level flags
- Maintain a versioned signal library with regular updates to address new bypass techniques
- Combine in-app heuristics with server-side Play Integrity / App Attest verification for defense in depth
Real-World Production Scenarios
Consider a mobile banking application with tens of millions of users. The threat model includes overlay attacks, credential harvesting via accessibility service abuse, and automated account takeover at scale. The appropriate response is not to block all rooted devices — that would create significant support volume from legitimate power users and developers — but to enforce graduated restrictions based on confidence score. Users with a low-confidence signal might have step-up authentication required for transactions above a threshold; high-confidence root signals trigger session termination and an out-of-band notification to the security team.
For a mobile gaming platform, the primary concern is emulator-based bot farms that automate resource acquisition and inflate leaderboards. Here, emulator detection feeds into a soft enforcement model: accounts detected as running in emulated environments receive resource acquisition rate limits and are excluded from competitive matchmaking but are not immediately banned. The rationale is that false positives — legitimate players who happen to use an emulated environment — should not be penalized harshly for a first offense. Escalation to hard bans happens after a pattern of behavior is confirmed.
Enterprise mobility management presents a third distinct scenario. A company deploying a document management application to employees' personal devices (BYOD) needs to comply with data loss prevention (DLP) policies. Here, rooted devices represent a genuine compliance risk: sensitive documents accessed on a rooted device could be extracted by malicious apps with elevated privileges. The appropriate response is typically to block access entirely from devices that fail integrity checks, but to do so via the MDM policy layer rather than in-app enforcement, ensuring consistency across the application portfolio.
A more nuanced scenario involves developer tooling distributed via the app stores. An application that targets developers — debugging tools, CI utilities, code review apps — will naturally have a disproportionately high percentage of users on rooted devices or emulators. Aggressive detection enforcement would block the exact audience the application is designed to serve. In this case, detection signals are valuable for telemetry and understanding the user population, but enforcement should be off entirely unless specific abuse patterns are observed.

Common Pitfalls and Failure Patterns
The most pervasive failure pattern in production detection systems is treating detection as a one-time implementation rather than an ongoing operational concern. The bypass landscape for root detection evolves continuously: Magisk updates its hiding capabilities, new kernel-level hooking frameworks emerge, and emulator platforms add hardware profile spoofing. An implementation that was effective two years ago may have a 40% false-negative rate against current evasion tools. Detection logic must be treated as a maintained component of your security architecture with regular review cycles tied to the threat landscape.
A second common failure is the false-confidence trap of running detection checks only at application launch. A sophisticated attacker can pass initial checks by delaying the attachment of an instrumentation framework until after launch-time validation completes. Detection should be periodic throughout the session lifecycle, with sensitive operations triggering their own verification rather than relying on a session-level pass obtained at startup.
Over-aggressive enforcement without careful false positive analysis damages user trust and generates disproportionate support costs. Rooted devices are not uniformly malicious — they represent a meaningful segment of power users, developers, and accessibility users who have legitimate reasons to modify their devices. Blocking these users wholesale, particularly without a clear in-app explanation or an appeals process, creates a support and reputational liability that often outweighs the security benefit for all but the highest-sensitivity applications.
- Treating detection as a static implementation rather than a maintained, versioned security component
- Performing checks only at launch rather than periodically throughout the session lifecycle
- Conflating detection confidence with enforcement certainty — high-signal detection still requires proportionate response
- Hardcoding enforcement thresholds in the binary, making policy changes require a full release cycle
- Failing to instrument false positive rates and user impact alongside threat detection metrics
Strategic Best Practices
A mature security posture around root and emulator detection requires both technical discipline and operational process. The technical architecture must be sound — layered signals, server-side policy, hardware-backed attestation where available — but the operational side is equally important: clear ownership, documented threat models, regular bypass testing, and defined escalation paths when bypass techniques are identified in the wild.
Start from a documented threat model rather than a checklist. This helps frame detection decisions in the context of your application's actual risk profile. Not every application requires the same depth of detection—the overhead of advanced behavioral analysis is rarely justified for a simple utility app. For guidance on structuring mobile app threat models, refer to the OWASP Mobile Application Security documentation.
Treat your detection library as a first-class dependency with its own release cycle. When a major bypass technique becomes public — a new Magisk module, a new Frida evasion pattern — you need to be able to deploy an updated detection response within days, not the three-to-six week cycle of a standard app update. This requires both a modular implementation that can be updated independently and a server-side configuration capability that allows behavioral adjustment without a binary release.
- Build detection as a versioned, maintained component — not a one-time implementation
- Separate detection confidence scoring from enforcement policy, keeping policy server-side and configurable
- Use hardware-backed attestation (Play Integrity API, App Attest) as the foundation for high-security contexts
- Instrument false positive rates and user impact metrics with the same rigor as detection rates
- Conduct regular red team exercises specifically targeting your detection implementation
- Align enforcement severity with threat model risk — graduated responses outperform binary block-or-allow logic
Conclusion
Root and emulator detection occupies an uncomfortable position in mobile security engineering: it is simultaneously one of the most important defensive layers available and one of the most operationally fraught to implement well. The technical community has spent years in an arms race between detection implementations and evasion frameworks, and that race has no foreseeable end. What has become clear from production deployments is that the goal of detection should not be impenetrability — no in-app mechanism achieves that — but rather raising the cost of attack to a level that makes mass exploitation economically unviable.
The engineers who implement these systems most effectively are those who have internalized the distinction between detection and enforcement. Detection is a probabilistic signal — a confidence score derived from a set of independent indicators, none of which is individually conclusive. Enforcement is a policy decision that must account for the full population of users who will be affected, including the legitimate users who will collaterally experience restrictions. The architecture that supports this distinction — layered signal collection, server-side policy engines, configurable thresholds, hardware-backed attestation for the most sensitive operations — is not merely an engineering preference but a prerequisite for running a production system responsibly.
The practical recommendation for most applications is to implement detection as a telemetry and risk-scoring mechanism from the start, even if enforcement is initially disabled. This gives you visibility into your user population's integrity profile, allows you to calibrate thresholds before making enforcement decisions that affect real users, and builds the operational muscle for managing the detection system as a living component of your security architecture. High-security applications — financial services, healthcare, enterprise data access — should layer in Play Integrity and App Attest as their attestation foundation, supplemented by in-app behavioral signals for defense in depth.
Root and emulator detection, done thoughtfully, is not about distrusting your users. It is about structuring your security architecture so that the adversarial population — fraud operators, bot farm operators, runtime attackers — faces a fundamentally different, higher-cost path than the legitimate user base. Getting that calibration right is the work. It requires ongoing investment in threat intelligence, regular bypass testing, careful false positive analysis, and a willingness to revise enforcement decisions as the threat landscape evolves. There is no static answer — only a continuously improved posture.



.svg)