Mobile applications operate in fundamentally adversarial environments. Unlike server-side software, a compiled mobile binary is distributed directly to end-user devices — devices that may be rooted, jailbroken, instrumented with dynamic analysis tools, or running inside emulators specifically configured for reverse engineering. The moment your APK or IPA leaves your build pipeline, it enters a space where the runtime behavior of your application is no longer guaranteed to match the behavior you tested and shipped. This is the core problem that Runtime Application Self-Protection (RASP) is designed to address.
RASP is not a single technology. It is an architectural philosophy — the idea that a mobile application should carry within itself the instrumentation needed to detect, respond to, and in some cases neutralize threats at the point where code executes. Rather than relying entirely on perimeter defenses like network firewalls, API gateways, or certificate pinning alone, RASP moves the security boundary inward. It embeds detection logic into the application binary and activates that logic at runtime, during actual execution, when the application has direct visibility into the conditions of its own execution environment.
For mid-to-senior mobile engineers, the practical implications are significant. Implementing RASP correctly requires understanding how your application interacts with the operating system at a low level, how debugging and hooking frameworks operate, and what the observable signals of tampering look like from inside a running process. Getting this wrong — either by missing critical attack surfaces or by implementing over-aggressive checks that degrade legitimate user experience — can have serious product and security consequences. This article provides the technical depth needed to reason about RASP architecturally and implement it defensively.

Foundational Concept: What RASP Actually Is
The term Runtime Application Self-Protection was coined by Gartner in 2012, but the underlying techniques predate that formalization considerably. At its core, RASP describes a class of security controls that are embedded within an application's own execution context, rather than deployed externally as a standalone product or infrastructure layer. The application monitors itself — checking the integrity of its own environment, verifying that it is executing as expected, and reacting when those expectations are violated.
On mobile, this manifests most commonly as a set of runtime checks distributed across an application's startup sequence, session lifecycle, and sensitive operation boundaries. These checks examine properties of the execution environment: Is the device rooted or jailbroken? Is the application's code the same code that was signed and shipped? Is there a debugger attached? Is the application running inside an emulator? Is a hooking framework like Frida or Xposed active in the process space? Each of these conditions represents a distinct threat model, and a well-implemented RASP system addresses them independently rather than collapsing them into a single binary decision.
The evolution of RASP on mobile has tracked the evolution of the attack tooling. Early implementations focused narrowly on jailbreak and root detection, reacting to the presence of known paths and binaries associated with tools like Cydia or SuperSU. As attackers matured, they began bypassing these signature-based checks using hooking frameworks, leading to a second generation of RASP that incorporated hook detection and process memory inspection. The current generation addresses a wider surface: emulator fingerprinting, code integrity verification via hash comparison, and behavioral anomaly detection that goes beyond static environment checks.
- Root and jailbreak detection via filesystem and API heuristics
- Debugger detection using ptrace state inspection and timing analysis
- Hook detection scanning process memory for known framework signatures
- Emulator fingerprinting from hardware identifiers and sensor data
- Code integrity validation through binary hash and signature verification
Why It Matters in Modern Mobile Development
The conventional argument for RASP centers on preventing fraud and IP theft, which remains valid. But the more nuanced argument, relevant to engineering teams building at scale, is about the assumption of trust that underpins most mobile architectures. API endpoints typically authenticate a user identity, but they rarely authenticate the application identity in any meaningful way. Attackers who can reverse engineer your binary, modify its behavior, and repackage it can create counterfeit clients that interact with your backend infrastructure in ways you never intended — bypassing client-side business logic, automating interactions at scale, or exfiltrating decrypted data.
This is particularly acute in fintech, healthcare, gaming, and e-commerce applications where the business logic running client-side has direct financial or regulatory consequences. In a banking app, a tampered binary might bypass transaction confirmation screens. In a gaming app, it might disable anti-cheat logic. In a healthcare app, it might exfiltrate decrypted patient data that the application is temporarily holding in memory. None of these attacks are hypothetical; they are documented in CVE databases and security research going back years.
From an engineering team perspective, RASP also intersects with release cycle and developer experience in ways that are worth thinking about explicitly. Runtime protection logic needs to be maintained across OS updates — behavioral signals that reliably detected emulators on Android 11 may be less reliable on Android 14. Integration with CI/CD pipelines for code integrity checking requires that signing workflows are stable and observable. These are not set-and-forget implementations.
- Prevents client-side bypass of business logic in high-value transaction flows
- Detects and blocks automated abuse from repackaged or modified applications
- Provides behavioral signals useful for fraud scoring and anomaly detection systems
- Reduces attack surface for decrypted in-memory data exfiltration
- Complements backend authentication without replacing it
Architecture & System Design Breakdown
A well-structured RASP implementation for mobile is organized into three functional layers: detection, response, and reporting. These layers are logically distinct, even if they share code. The detection layer is responsible for gathering signals from the runtime environment. The response layer decides what to do with those signals. The reporting layer communicates findings to backend infrastructure for monitoring and incident response. Coupling these concerns tightly is one of the most common architectural mistakes teams make, and it results in systems that are difficult to tune and impossible to audit.
Detection logic itself should be organized around threat categories rather than specific detection methods. Each threat category — tampering, debugging, emulation, hooking, integrity — will typically have multiple independent detection probes contributing signal. Combining these signals using a weighted scoring model, rather than treating any single detection as a binary trip wire, significantly reduces both false positive rates and the effectiveness of targeted bypasses. An attacker who disables one probe may not have disabled all probes contributing to that threat category's score.
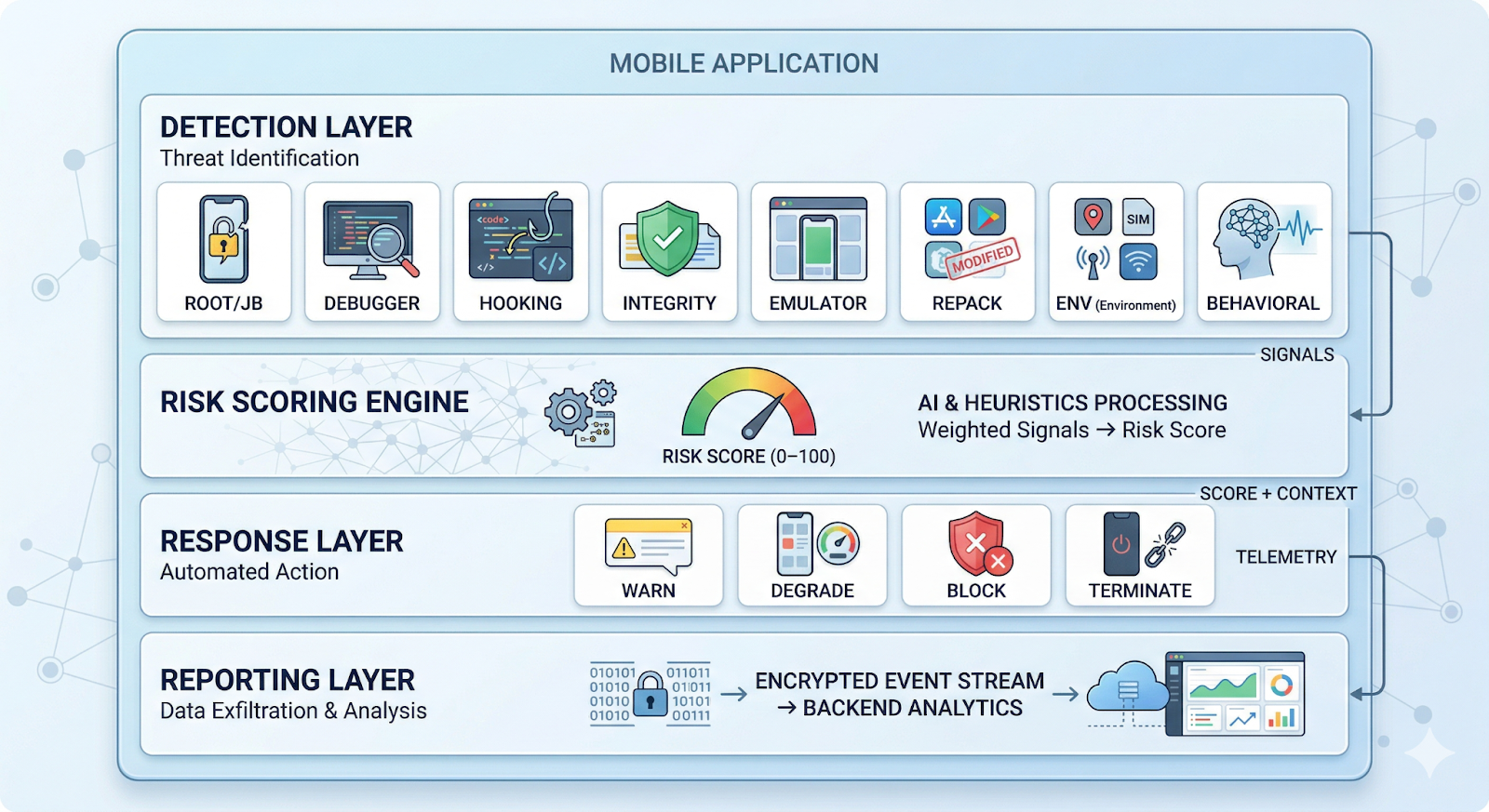
- Detection probes are stateless and independently executable
- Risk scoring is configurable server-side to avoid requiring app updates for tuning
- Response behaviors map to score thresholds, not individual probe results
- Reporting is asynchronous and does not block the main execution thread
- All three layers have independent test surfaces
Implementation Deep Dive
The implementation of RASP begins at the application startup phase, before any user-facing initialization. On Android, this means placing detection logic in the Application.onCreate() override or, for more comprehensive coverage, in a native library loaded via System.loadLibrary() before JVM initialization completes. On iOS, equivalent early-startup placement is typically achieved through static initializers in Objective-C or early @_silgen_name hooks. Starting early matters because some attack tools can only be defeated if you observe them before they have fully instrumented your process.
Hook detection deserves particular attention in the implementation phase. Frida, the most widely used dynamic instrumentation toolkit, works by injecting a JavaScript engine into a target process and patching function prologues with unconditional jumps to its own trampoline stubs. The detectable signal is the modification of the first bytes of hooked functions — on ARM64, a legitimate function prologue begins with a known instruction sequence, whereas a Frida-patched prologue begins with an unconditional branch (B instruction, encoding 0x14xxxxxx). Scanning critical function prologues in memory for this signature is a reliable first-order detection technique. See the Android NDK security guidance for native memory access patterns relevant to this approach.
For code integrity, the most robust approach combines APK/IPA signature verification with a hash of the compiled binary itself. The application should verify at startup that its own signing certificate matches the certificate used in production. On Android, the PackageManager API exposes the signing certificate chain, which can be compared against a pinned certificate hash embedded in the application's native library — not its Java code, which is easier to modify. On iOS, the corresponding mechanism is the SecStaticCodeCheckValidity API.
A numbered implementation sequence for a production RASP integration:
- Environment pre-scan: Before JVM/Dart initialization, load native library and scan for Frida gadget, Xposed framework modules, and substrate hooks in /proc/maps on Android.
- Device integrity check: Query root/jailbreak indicators — known binaries, world-writable /system partitions, SUID files, and iOS SpringBoard entitlement anomalies.
- Emulator fingerprinting: Compare hardware identifiers (IMEI, MAC address, sensor availability) against known emulator profiles. High-confidence emulator presence should be logged even if not immediately blocking.
- Code integrity verification: Hash the application's compiled binary and compare against a known-good value distributed via a separately pinned endpoint, not bundled in the binary itself.
- Debugger attachment check: Use ptrace(PTRACE_TRACEME) on Android to detect a pre-attached debugger. On iOS, call sysctl with CTL_KERN/KERN_PROC/KERN_PROC_PID and check the P_TRACED flag.
- Risk scoring and response: Aggregate signals into a risk score. Ship the score to the backend with the session token. Apply the configured response policy — warn, degrade, or block — based on current server-side thresholds.
// Android NDK -- minimal hook detection probe bool detectFridaHook(void* funcPtr)
{ uint32_t* code = reinterpret_cast<uint32_t*>
(funcPtr); // ARM64 unconditional branch: top 6 bits == 0b000101
return ((*code >> 26) == 0x05); }
Advanced Patterns & Optimization
One of the most important advanced patterns in production RASP is the use of server-side configuration for response policy. The question of whether a detected condition should produce a warning, a degraded experience, or a hard block should not be hardcoded into the binary. Mobile application deployments span enormous diversity in device states — legitimate devices running custom ROMs, enterprise devices with modified certificates, security research environments. The ability to tune response thresholds without a new app release is essential for managing false positive rates, especially in the weeks following a major OS update that changes the behavioral baseline.
A related pattern is the distribution of detection probes across time rather than concentrating them at startup. Performing all checks during application initialization creates a predictable, discoverable target — an attacker profiling your app with a memory dump knows exactly when and where to look. Probes that are re-evaluated at unpredictable points during the session (during API calls, during UI transitions, at randomized intervals) are significantly harder to systematically disable. This pattern is sometimes called temporal dispersion, and it is described in depth in the OWASP Mobile Application Security Verification Standard.
Anti-tampering instrumentation should itself be obfuscated. Detection logic that is clearly labeled and easily identifiable in a decompiled binary provides an attacker with a roadmap to bypass it. String obfuscation, control flow flattening, and opaque predicate insertion all reduce the legibility of RASP code in static analysis. These techniques have performance costs, and they should be applied selectively to the security-critical paths, not the entire application.
- Use server-side configuration for response policy to enable tuning without app releases
- Distribute probe execution temporally to defeat timing-based analysis
- Apply obfuscation selectively to detection logic, not the entire codebase
- Combine multiple independent probes per threat category for scoring resilience
- Use native (C/C++) code for the most sensitive detection logic to raise the reverse engineering cost
Real-World Production Scenarios
Fintech transaction signing. A mobile banking application uses RASP to validate the execution environment before allowing the cryptographic signing of payment transactions. If hook detection fires above a threshold score, the transaction signing key material (held in Android Keystore or iOS Secure Enclave) is not released, and the user is asked to re-authenticate via a step-up flow. This architecture accepts that detection is probabilistic rather than binary — the goal is not to prevent all attacks but to raise the cost of reliable, scalable ones.
Gaming anti-cheat. A competitive mobile game uses RASP alongside its backend anti-cheat systems to shorten the gap between cheat deployment and server-side detection. On the client, RASP identifies the presence of memory editors (such as GameGuardian and similar tools) and sends session telemetry to the backend before the cheat can significantly impact gameplay outcomes. Importantly, the game does not terminate upon detection—instead, it continues running while flagging the session for backend review. This approach minimizes false positives and prevents attackers from calibrating their cheats against immediate termination signals. For implementation patterns around device integrity and secure telemetry, refer to the Google Play Integrity API documentation.
Enterprise MDM compliance. A regulated enterprise application uses RASP to enforce mobile device management policy independently of the MDM infrastructure. The application checks device integrity signals and refuses to decrypt sensitive documents if the device has been removed from the MDM enrollment or if root indicators are present. This provides a defense-in-depth layer that does not depend on the MDM client remaining installed or functional — a genuine concern in BYOD environments.
API abuse prevention. A consumer marketplace application uses RASP detection data as an additional signal in its fraud scoring pipeline. Rather than using RASP as a hard gate, each session's RASP telemetry (emulator likelihood, hook detection score, code integrity status) is passed to the backend as metadata alongside API calls. The backend risk engine uses this to adjust the scrutiny applied to actions like account creation, listing creation, and payment initiation — providing a risk-proportionate response without generating user-facing friction in legitimate sessions.
Common Pitfalls and Failure Patterns
The most damaging implementation mistake in RASP is hard-blocking users based on low-confidence signals. This generates support escalations, app store reviews, and in regulated industries potentially compliance exposure if legitimate users cannot access required services. Root detection is particularly prone to this problem because a significant population of Android users run legitimate custom ROM configurations, especially in markets where carrier-locked devices are common. A system that terminates the application on any positive root indicator, without scoring or context, will block more legitimate users than attackers in some demographics.
A second common failure is concentrating security-critical detection logic in Java or Kotlin managed code without native reinforcement. Managed code running on the ART virtual machine is significantly more accessible to dynamic instrumentation than native code. Java method hooks via Xposed, ART method replacement, and Frida Java bridges all operate at the managed code layer. Detection logic implemented only in Java can be bypassed by hooking the detection function itself and returning a clean result. Moving critical probes to the NDK layer, and verifying the results of managed-code checks from native code, substantially raises the cost of bypass.
Inadequate maintenance cadence is a structural risk that accumulates over time rather than presenting as an acute failure. The Android and iOS platforms both evolve in ways that break existing detection heuristics — emulator detection signatures shift with emulator version updates, and jailbreak detection for new iOS versions requires new probe logic to be written and shipped. Teams that treat RASP as a one-time implementation without ongoing maintenance find that their detection fidelity degrades quietly until it is largely ineffective.
- Hard-blocking on low-confidence signals generates unacceptable false positive rates
- Placing all detection logic in managed code exposes it to ART-layer hooking
- Lack of server-side tuning capability forces app releases to adjust thresholds
- Bundling the known-good binary hash inside the binary creates a circular integrity problem
- Neglecting post-launch maintenance as OS versions change invalidates detection heuristics
Strategic Best Practices
Effective RASP deployment is as much a product decision as a technical one. The threat model should be written down, reviewed, and agreed upon before a line of detection code is written. Which threat categories matter for your application? What are the acceptable false positive rates for each response tier? What is the process for handling a detection event that turns out to be a false positive? These questions have answers that vary by application domain, and they must be resolved before implementation to avoid architectural regret. The Apple Platform Security Guide provides useful context for the iOS threat surface that should inform this analysis.
Testing RASP logic requires a dedicated quality engineering effort that is distinct from normal functional testing. Detection probes need to be validated both positively (do they fire when the condition they detect is present?) and negatively (do they remain quiet when the condition is absent?). Building an internal test harness that can simulate the signals of a hooked process, a rooted device, and an emulator environment — without requiring actual attack tooling — is a significant investment but necessary for maintaining confidence in detection fidelity as the codebase evolves.
Integrating RASP telemetry with your backend observability stack from day one is essential. Detection events that are logged only on-device have no forensic value after the session ends. Encrypted, authenticated telemetry sent to a backend where it is correlated with session and user signals enables the kind of abuse pattern analysis that makes RASP genuinely useful for fraud prevention. Consult the Android App Security Best Practices documentation for guidance on secure telemetry transmission patterns on Android.
- Document the threat model explicitly before implementation begins
- Use weighted risk scoring rather than binary detection flags for all response decisions
- Implement detection probes in the NDK for the highest-sensitivity threat categories
- Test both detection accuracy and false positive rate in a controlled lab environment
- Ship RASP configuration as server-side policy to decouple tuning from release cycles
- Treat RASP telemetry as a first-class input to backend fraud and abuse scoring systems
Conclusion
Runtime Application Self-Protection is not a magic barrier — it is a detection and response layer designed to raise the cost and complexity of client-side attacks to the point where they are no longer economically viable at scale. The most important conceptual shift for engineers approaching RASP for the first time is moving away from the binary security mindset of "protected or not protected" toward a risk-scoring mindset in which the question is always: "What is the confidence of our detection, and what response is proportionate to that confidence?" This reframing changes how you design detection architecture, how you write response logic, and how you manage false positive rates across a diverse user population.
The technical depth required for production RASP — native code development, process memory inspection, binary integrity verification, instrumentation detection — sits at the intersection of systems programming and application security. It is not work that can be done well by a team that has not invested time in understanding how the mobile operating systems actually execute code at the native layer. For teams without that expertise, using a well-evaluated third-party SDK for baseline detection is a reasonable starting point, provided the SDK is evaluated as critically as any other security-sensitive dependency.
Maintenance is the unglamorous factor that determines whether a RASP implementation remains effective over time. Every major iOS and Android release should trigger a re-evaluation of detection probe accuracy. Every new version of major hooking frameworks — Frida, Xposed, Substrate — should be added to the test matrix. Threat modeling is not a one-time activity. The adversary tools your RASP is designed to detect will evolve, and your detection logic must evolve with them. Teams that build RASP with this maintenance reality factored into their resourcing have significantly better outcomes than those that treat it as a completed feature.
Ultimately, RASP is most powerful when it is part of a layered defense strategy rather than a standalone control. Combined with certificate pinning, server-side request authentication, behavioral anomaly detection at the API layer, and a mobile threat intelligence feed, it becomes part of a system where the failure of any single layer does not result in a complete compromise. Building that layered system, and maintaining each layer, is the actual work of mobile application security — and RASP is one of the most important layers to get right.



.svg)